We need to talk about privacy
Society needs to debate how Intelligence Services operate and reform laws designed for another era.
The Snowden leaks have been a hot topic of conversation in the pebble office. Our office is located just a short walk away from the SIS Building in Vauxhall that houses MI6 and we are just around the corner from a former SOCA building too. We know of contacts who work at businesses that they could not name and as technicians we understand the techniques that the leaks have exposed.
The majority of the debate has not been about technology though. It has been around the level of surveillance and whether this is acceptable in a democratic society.
Prism ¶
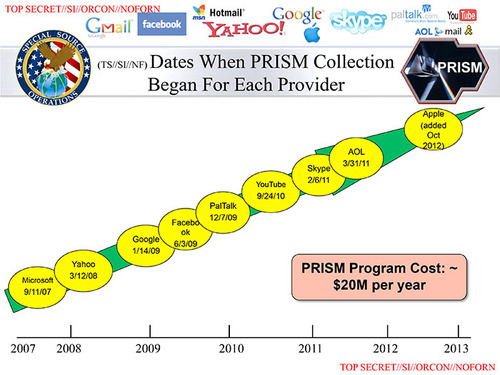
Prism was the first program to be exposed and allows the NSA to request data from Internet businesses via agreed back doors into the data of major Internet businesses. Any data that matches court-approved search terms must be handed over to the agency. The slides detail the number of Internet businesses involved including Microsoft, Yahoo!, Facebook, Google, Apple and Dropbox. These businesses denied a complicit programme and many have subsequently issued transparency reports around the issue. The idea that data held in the cloud can be requested by intelligence agencies when they have a court order seems acceptable. The idea that Intelligence Agencies have direct access to the data is not.
MUSCULAR - The Smiley Face ¶
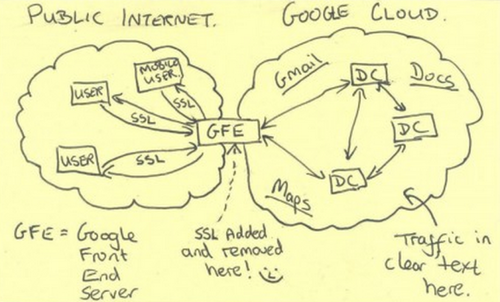
The MUSCULAR project was exposed as a way for the NSA to harvest entire data flows passing through fibre optic cables and switches that link Google Data Centres. Effectively this enables covert snooping of all data that passes through Google’s Cloud. According to reports 181,280,466 records were collected from Google and also Yahoo in a period of 30 days. The sketch that was published ont the web revealed a smiley face celebrating the hijack. It smacked of a calling card after a robbery.
As a direct result of this disclosure we have seen one of our major clients decide not to deploy Google Apps into their business for fears around privacy. Several staff are migrating off Google Apps.
Lavabit ¶

After the initial leaks were published Lavabit became a target for Intelligence Agencies. It is thought Snowden had used the service to email journalists about releasing the leaks. Lavabit is an encrypted email service and was asked to hand over SSL keys by the federal government. As a result Lavabit decided to suspend the service as its entire business model was compromised. This particular story generated disquiet but there are some issues with the technology here. The fact that the a site is encrypted with a single SSL private key means that once that key is compromised everything is compromised. The model is that intelligence agencies cannot request any information without compromising everything. Ladar Levinson, the founder of Lavabit continues to take a firm stand on privacy and is on a funding drive to take this forward.
Sub-standard Journalism ¶
Technology editors at newspapers have historically been tasked with reporting on technology innovations and product launches. The Snowden leaks are a totally different test of these journalistic skills, and in many cases reporting from traditional media outlets has been severely lacking. A recent Telegraph article suggested that exposing the surveillance capabilities could lead to Paedophiles escaping the police.
Paedophiles may escape detection because highly-classified material about Britain’s surveillance capabilities have been published by the Guardian newspaper, the government has claimed.
A similar level of scaremongering was leveled around the introduction of the 90 day detention law. What is depressing is that there is no discussion of whether the level of surveillance is acceptable. Words like ‘Terrorist’, ‘Traitor’ and ‘Paedophile’ tend to be used whenever any questions around the intellegence agencies activities. Yes, the intelligence agencies do need powers but it is the job of journalists to question assumptions and to probe for the truth rather than nodding like an obedient dog.
Sub-standard political scrutiny ¶
Politicians are at fault too. Yesterday a toothless Intelligence and Security Committee in London asked questions of the heads of the British Intelligence Agencies. There questioning was broadly along the lines of ‘Have you done anything wrong’. The answer was ‘No, and we have been compromised’. At this point the committee seemed to say ‘Ok. Carry on then.’ To anyone watching the whole exercise must be considered pointless.
Not long after journalists in the UK sparked ourage with phone hacking practices it emerged intelligence agencies were tapping leaders of Allied states. There seems to be little understanding among politicians around what is an isn’t acceptable for their intelligence agencies around this issue. The Agencies operate within laws that were not designed for the Internet age and with a level of transparency that was designed for the cold war. Put simply for everyone to move forward this cannot continue.
Two cultures coliding ¶
In the context of these leaks we are seeing two worlds collide. The open, free Internet that was originally designed for academics and researchers to exchange information and the shadowy world of spying.
The web has disrupted business models, toppled governments, and it is democratising power structures everywhere. In short it is eroding power structures where a single point of authority is in effect. Ironically it also provides the architecture for intellegence agencies to theoretically monitor all of it. The dynamic is neatly summarised by Tim Berners-Lee, the inventor of the World Wide Web.
Whistleblowers, and responsible media outlets that work with them, play an important role in society. We need powerful agencies to combat criminal activity online – but any powerful agency needs checks and balances and, based on recent revelations, it seems the current system of checks and balances has failed.
This for me is the clearest expression of how as a society we need to move forward. Intelligence agencies can no longer operate under a legal framework designed for another age. Citizens expect increasing levels of transparency from the governments that serve them and the businesses they work for. Our politicians, journalists and agencies must debate privacy thoroughly in an open manner. An assessment must be made of what has happened and a decision made on whether the intelligences agencies are operating within existing laws or, as some civil liberatarians are suggesting, are totally out of control. In short it is time for citizens, politicians, journalists and agencies to talk openly about privacy.
Tags
Can you help make this article better? You can edit it here and send me a pull request.